The Slick VPN Guide to Staying Safe on the Internet – Part 2 of 7: Threats to Personal Privacy of Children
The Internet, Online Privacy, and Connected Toys
If you look up the definition of what the internet is, you’ll find something like the below:
The internet is an interconnected network of computers located all across the globe that provides information via standardized communication protocols
So anyone on the internet is, by definition, interconnected to a global network whose stock in trade is information.
Small wonder that people have privacy concerns when online. An individual’s private information is most definitely not something anyone wants available to a global network. But does that mean you should avoid the internet completely?
Absolutely not. First of all, it would be nearly impossible today. But secondly, the internet can help an individual accomplish a great deal of good—provided they understand and use it properly.
But what if that hacking threat is aimed at a child, and disguised as a toy?
Online Privacy Fears
Imagine hacking—a very adult activity—happening in the guise of childhood toys. Despicable? Yes, but it not only could happen but has— twice with Teddy bears alone.

CloudPets manufactures connected plush toys that use the internet to play games and record and deliver messages to or from parents or loved ones and children. But the company had a security breach, with the login records of nearly a million customers stolen, reported Vice. That meant the millions of recordings sent through the toys were suddenly easy prey for the hackers as well.
And that wasn’t the first Teddy bear hack— nor will it likely be the last.
Talking bears from Fisher Price were hacked at the operating platform level, which meant the names and birthdays of children using the toys was suddenly available. Anyone who knows about identity theft know that a name and birthday is ¾ of the way towards creating an identity based on those credentials.
Even beloved Barbie dolls are potentially hackable—if they are connected to the internet—and could become surveillance devices aimed at gathering sensitive information.
No one can expect children to protect themselves against this kind of breach. So Parents who are looking at purchasing an “Internet of Things” (IoT) toy want to make sure they educate themselves to the set-up steps and use passwords—strong passwords. These connected toys are going to become more common, and without paying close attention, so could hacking incidents involving toys and children.
Rules for Internet “Connected” Toys:

Turn off connected toys when not in use—do not leave them connected to the internet.

Don’t allow young children on the internet—even via toys—unless supervised by an adult.

Check closely any toy’s application that seeks to collect data like addresses, birthdays, full names, or the like. There’s a lot of harm that could be caused by doing so—and little benefit.

Passwords should be maintained by parents—not children—even, and perhaps especially—for toys, games, or websites used by children.

Go ahead and Google it: check that toy out to see if there are known security risks.

Watch out for Bluetooth in public places. A toy with Bluetooth—much like your smartphone data—could be hacked when in an airport, school, mall, or similar public venue.

Only use secure and trusted WiFi networks—like in your home.

There are home network protection solutions that can help prevent malware, stolen passwords, and spying through IoT devices- including toys.
What else can you do?
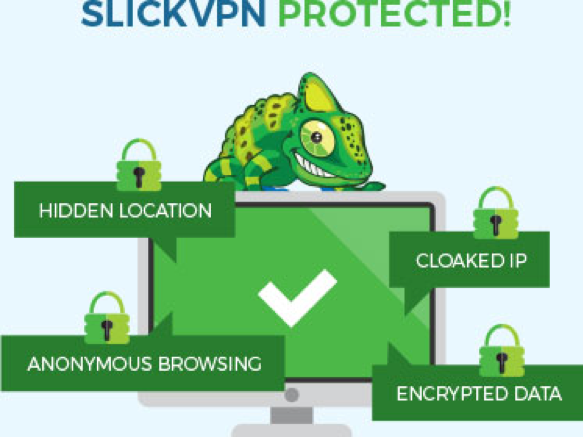
Children and the elderly are, unfortunately, the most prone to the often silent dangers online. Help protect them with a good VPN service like SlickVPN.
A VPN encrypts all your data, and masks your IP address. Hackers can’t use encrypted data, and if they don’t know your IP address they can’t hone in on you.
When you are connected to the internet with SlickVPN, you enjoy complete privacy. No one can monitor what you do online. No one can throttle and slow down your connection. You’ll surf completely anonymously, and with the highest possible quality…
The strong encrypted tunnel produced by SlickVPN means the addresses or URLs of any site you visit are masked, as well as any unique identifiers for you. So you can stay safe online.